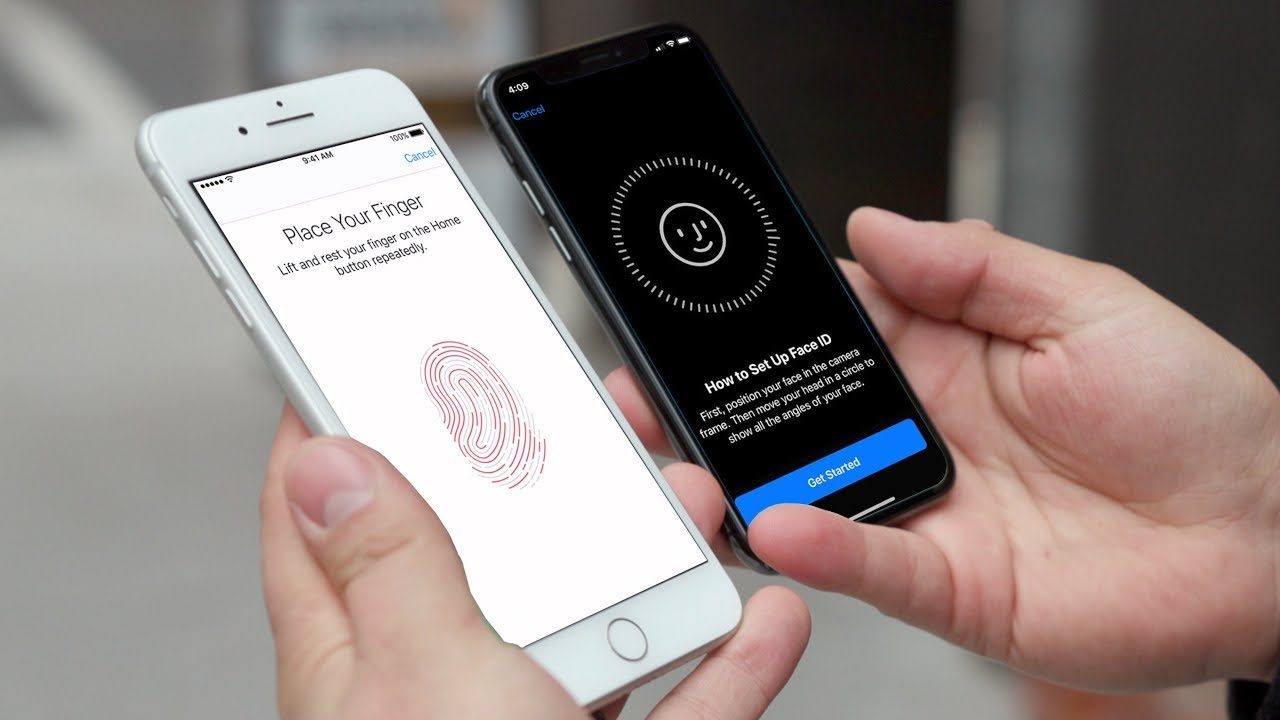
Preventing other people from accessing private information in our smartphones is a major concern for many people. This is why mobile phone manufacturers have made efforts to simplify device locking and its corollary, secure unlocking. Now, many Android smartphones have an integrated fingerprint reader hidden directly under the screen. As for iPhones, they can be unlocked more naturally by putting your face in front of the screen, thanks to Face ID technology.
The fingerprint reader or face recognition are also used to secure access to banking applications or authorize payments in the App Store and the Play Store, the Apple and Google application stores. Unfortunately, a slew of recent issues has raised concerns that these digital safeguards may be more vulnerable than we thought.
Table of Contents
Samsung fingerprint ID issues
At the beginning of October 2019, a user from England observed that the fingerprint reader of her Samsung S10, which is directly accessible on the screen, failed to perform when the phone was fitted with a full transparent silicone shell. The user’s husband managed to unlock the phone. We were unable to reproduce this issue, but Samsung has acknowledged its existence. The Korean manufacturer believes to have identified its cause: the owner’s fingerprint got imprinted in silicone since the shell was very flexible. On October 23, Samsung made a software remedy available to its Korean customers. The manufacturer advises against the use of transparent front and back protections until consumers worldwide can download the patch.
This is not the first time that a Samsung smartphone has been criticized for its security weaknesses. For years, the homemade face recognition system could be tricked by showing it a simple video of the user.
Failures at Google and Apple
For its part, Google has equipped its new smartphone, the Pixel 4, with a very sophisticated facial recognition system inspired by that of the iPhone: it combines a projector of light points invisible to the naked eye and two infrared cameras. This allows you, for example, to be able to unlock your smartphone by looking at it at night.
But this security can be bypassed easily: just wait for its owner to take a nap and place the smartphone in front of his face. Unlike many other smartphones, the Pixel 4 doesn’t verify that its user’s eyes are open before unlocking.
There are also bugs. For example, we have witnessed a problem with the security system on Apple’s side. A child was able to unlock an 11-inch iPad Pro running iOS 13.1.2 protected by his parents’ Face ID technology.
Caution is required
These flaws, or these software errors, have one thing in common: to take advantage of them, you don’t have to be a security expert, you don’t have to mold a finger or sculpt a face. Anyone who finds these flaws can benefit from them. Biometric protection is not completely foolproof, and it’s an issue that goes beyond simply unlocking devices.
To better protect yourself, should you go back to more traditional methods such as the four or six-digit code? Not necessarily, because this way of unlocking smartphones is laborious, so it pushes you to adopt a code that is easy to guess. In addition, it is perfectly possible for someone to watch you enter the code and memorize it. Should we then replace the password with a diagram that we draw on the screen, as Android offers? Better to avoid: this method was deemed to be even less safe by a joint study of the University of Maryland and the United States Naval Academy.
In the absence of a better solution, it is better to rely on face and fingerprint recognition while avoiding giving them excessive confidence. Take time to check that other people can’t unlock your phone every now and then and don’t leave these devices lying around unattended.