Check if your antivirus can stop these 5 test malware files

Web app pentest provider: what they do and why you need them?

Network penetration tester salary

Top 4 secure messaging apps for smartphones

5 massive cybersecurity breaches caused by company employees

9 types of computer malware you didn’t know about

A complete guide to NIST cybersecurity framework

DOS and DDOS attack penetration testing – how is it done?

Big data security – is your data really safe?

PCI compliance – what is it and who needs it?

Endpoint security: everything you need to know

Spear phishing – one of the biggest cybersecurity threats

The ultimate guide to cloud encryption of data

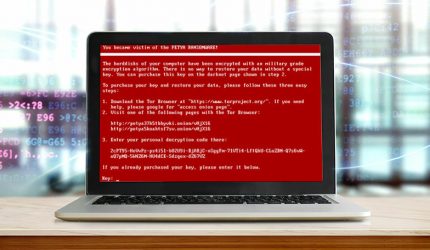
5 worst ransomware attacks throughout history

How to prepare for a physical penetration test?

How much does a penetration test cost?

5 things everyone needs to know about Smishing attacks

How to conduct a network vulnerability assessment?

Differences between external and internal penetration tests explained

Vulnerability assessments – everything you need to know
Wireless penetration test – the key to secure WiFi

6 best infosec and cybersecurity organizations

Managed security services for businesses and organizations

Hackers Found a Vulnerability and Attacked Microsoft: How to Protect your Business from Cybersecurity Threats

What is DTLS and how is it used?

Business mobile devices – how to secure them?

4 best internet browsers to protect your privacy

Device fingerprinting: the latest threat to online privacy

5 easy tips to secure your business WiFi
4 biggest email cybersecurity threats of 2021

Everything you need to know about the WhatsApp phishing scam

How to make business video calls safe?

Top 4 cybercrime and cybersecurity trends of 2021

Everything you need to know about DDOS attacks

6 best cybersecurity and privacy apps

How do you secure your WordPress website?

Has my phone been hacked? Find out!

Can you get a virus on YouTube? Find out here!

Is WhatsApp safe to use?

Using a password manager: is it safe?

5 best password managers for everyone
How to find out if my passwords have been stolen?

How to shop online safely?

My email account was hacked: what now?

Most common passwords in the world – is yours on the list?

New Instagram vulnerability exposed – protect your account now!

What is a CPN number and how do I get one?

How to keep your Twitter account safe from hackers?

How to protect my Instagram profile from being hacked?

How to protect my Facebook account from being hacked?
HackControl does not only provide cybersecurity and brand protection services to companies and organizations. We also work hard to educate our clients and the general public on the importance of cybersecurity, various cybersecurity threats that exist today and action your business or you personally can take to minimize those threats. In our cybersecurity blog, you will find hundreds of useful and easy to understand articles about phishing, social engineering, different types of hacker attacks, penetration tests, cyber insurance and more. We add new articles to our blog almost every week, so even if you can’t find the information you’re looking for now, remember to check in later to see if we cover your topic in the future or contact our specialists for a consultation.