Every year businesses lose more and more money due to cyber attacks. In the past few years, it has become clear that not even the largest companies are safe – a number of large-scale hacks have proven that even companies with virtually unlimited resources and reach are not paying enough attention to cybersecurity. In light of this, businesses are starting to take advantage of all the cybersecurity tools and techniques that are available, with vulnerability assessments exploding in popularity.

Table of Contents
What is a vulnerability assessment?
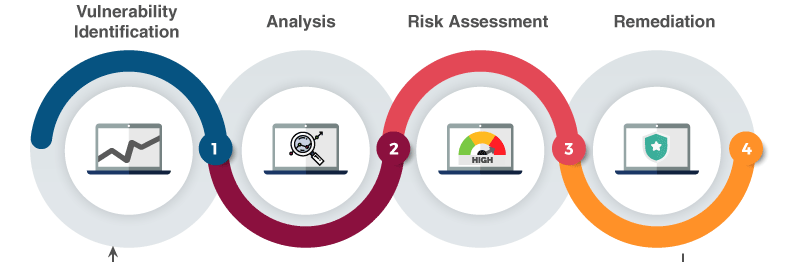
A vulnerability assessment or a vulnerability scan is a cybersecurity method during which experts use hacking tools to log into your company’s system, create a map of the system and build an inventory of all the items in the system. The cybersecurity expert then analyzes the results, compiles a list of all the vulnerabilities found in the system and creates a report and a remediation strategy which are then given to the company’s own cybersecurity team and management.
How much do vulnerability assessments cost?
The cost of conducting a vulnerability assessment depends on the type of environment that needs to be scanned, the number of IPs and servers involved in the scan, as well as the frequency with which the scans are performed (many companies charge less for regular scans). On average, you can expect to pay between 2,000 and 2,500 dollars.
Is it necessary to perform frequent vulnerability assessments?
On average, it’s best to perform vulnerability scans at least once every quarter. However, depending on the nature of your business, government requirements in the field, information sensitivity and changes to infrastructure, you may need to perform vulnerability scans every month or even every week.
How long do vulnerability scans take?
A typical vulnerability scan takes between 20 minutes to an hour to complete, while a web scan usually takes 2 to 4 hours. If you need to perform vulnerability assessments frequently, they can be carried out by your company’s internal security team or network administrator.
Do vulnerability assessments disrupt the regular course of business?
Yes, in most cases, vulnerability assessments will have a negative effect on the bandwidth and system performance. As a result, it’s best to conduct vulnerability scans outside of normal business hours. However, all of the devices should be left powered on and connected to the network if your goal is to get complete results.
What tools are used during vulnerability assessments and scans?
There are a number of different software programs that can be used to conduct vulnerability scans depending on the exact goals and task specifics. For instance, Nessus is a program specifically created to reduce the time and effort necessary to conduct vulnerability assessments. Netspark is a piece of software used to automatically conduct website application tests and identify SQL injection attacks and cross-site scripting.